Cybersecurity E-Learning for Employees
Cybersecurity E-Learning for Employees
Cyber threats are no longer the prerogative of IT departments. Any employee with a single click on a link, an email attachment or logging in to a corporate system is a potential point of entry by malicious actors. With the increasing rate of digitization of the operations of organizations at a pace never witnessed before, the human factor continues to be the most vulnerable link in any security chain. This fact has seen cybersecurity e-learning training turn out to be one of the most significant investments that a company may make in the present day.
Conventionally, security training has been conducted in classrooms, which has been found to be ineffective for the current workforce. Once-a-year sessions, in many cases in the form of thick slide presentations, seldom lead to permanent behavior change. Within days, employees forget what they learned, and the unchanging format can not take into consideration the rapidly changing threats. The e-learning training on cybersecurity bridges this gap by providing specific, flexible, and measurable learning experiences that can be incorporated into the daily workflow.
This paper discusses the ways organizations can successfully integrate cybersecurity e-learning programs that will safeguard the business and its employees. The advice here is directed at junior to mid-level professionals who may either be designing interactive e-learning content or seeking to integrate risk management training into their daily workflows.
Why Traditional Security Training Falls Short
The conventional method of employee security education, which was used over the years, consisted of an annual compliance workshop, a printed handbook and a multiple-choice quiz at the end. Although such practices served the purpose of checking regulatory boxes, these practices seldom translated into safer working practices. It has always been found that those employees who are only trained once a year are much more likely to be fooled into falling prey to phishing training than those employees who receive continuous training in a scenario-based approach.
The case described in detail in one of the mid-sized financial services firms in Australia clearly shows this issue. The company had to endure a data breach that has been dated to a finance employee who has been found to have clicked on an email of a fraudulent invoice. An analysis of the incident after it happened showed that the employee had taken the compliance training within the three months before the incident but had not internalized the warning signs of a phishing attack because the training had been done using only text-based slides with no practical exercises.
It is this disconnect between the learning of knowledge and its behavioral implementation that has seen cybersecurity e-learning training shift towards more interactive formats. Employees are much more prone to discern and react properly to actual threats when the training is interactive, contextual and repeated in short bursts. This has not merely been an educational choice, but a security enhancement, which can be measured.
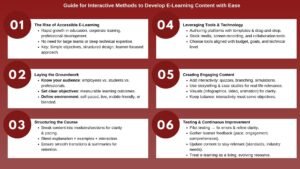
Designing Effective Interactive E-Learning Content
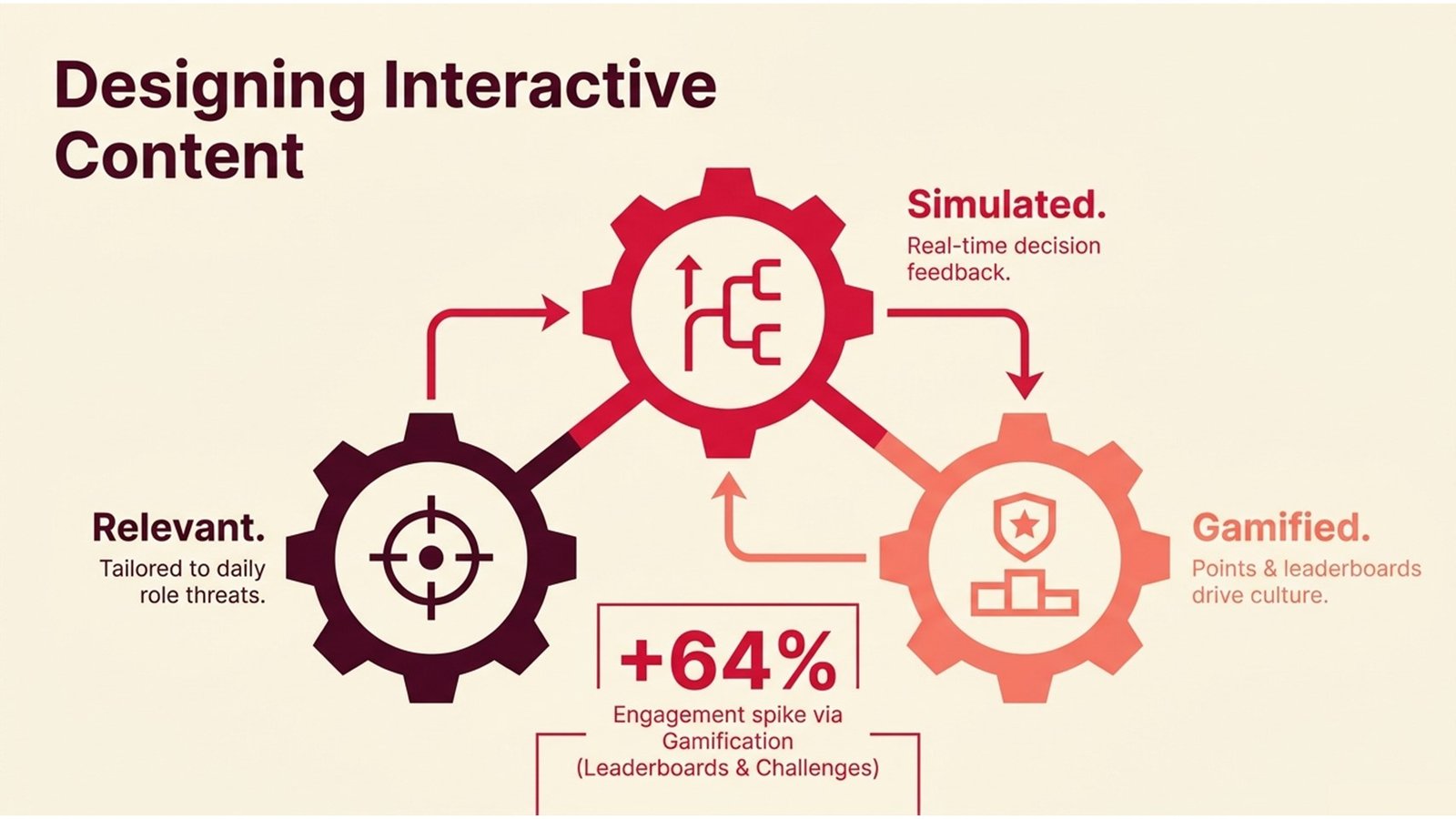
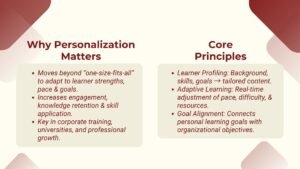
The level of involvement with the interactive e-learning content depends on whether the employee is able to interact with the content and work through the lesson or just clicks through to get his/her completion certificate. Designing is all about having a background of the context of the learner. The threats experienced by a customer service employee are not the same as those faced by a software developer or a senior executive. Role-based learning paths will ensure that every employee is exposed to situations that are pertinent to their day-to-day duties and make the training seem meaningful as opposed to generalized.
One of the most beneficial formats of cybersecurity training is the scenario-based format. Instead of introducing a rule and asking employees to memorize it, these modules put the learner into a simulated environment – a suspicious email has been received, a workmate needs sensitive information over an unknown channel or a device is found unlocked in an open place. The learner has to make a decision, and the system will instantly present the outcome of such a decision. It is this feedback loop that is what makes information instinctive.
Gamification features, such as points, leaderboards, progress badges, and time-limited challenges, help to increase engagement further. A technology company in Canada claimed that its security awareness program had radically improved the rate of completion of modules by redesigning its security awareness program to incorporate a monthly phishing simulation leaderboard. The workers got committed to ensuring that they increased their scores, and the healthy competition inevitably led to discussions on the security practice across groups. The interactive e-learning content of this type brings about a culture of security awareness, rather than a culture of compliance.
Table 1: Comparison of Security Training Formats
| Training Format | Engagement Level | Retention Rate | Best Suited For |
| Annual Classroom Workshop | Low | Low (fades within weeks) | Regulatory compliance baseline |
| Static E-Learning Slides | Low–Medium | Medium | Policy awareness, onboarding |
| Scenario-Based Modules | High | High | Threat recognition, decision-making |
| Gamified E-Learning | Very High | High | Ongoing culture-building |
| Phishing Simulations | High | Very High | Practical behavioral reinforcement |
Embedding Risk Management Training into the Learning Journey
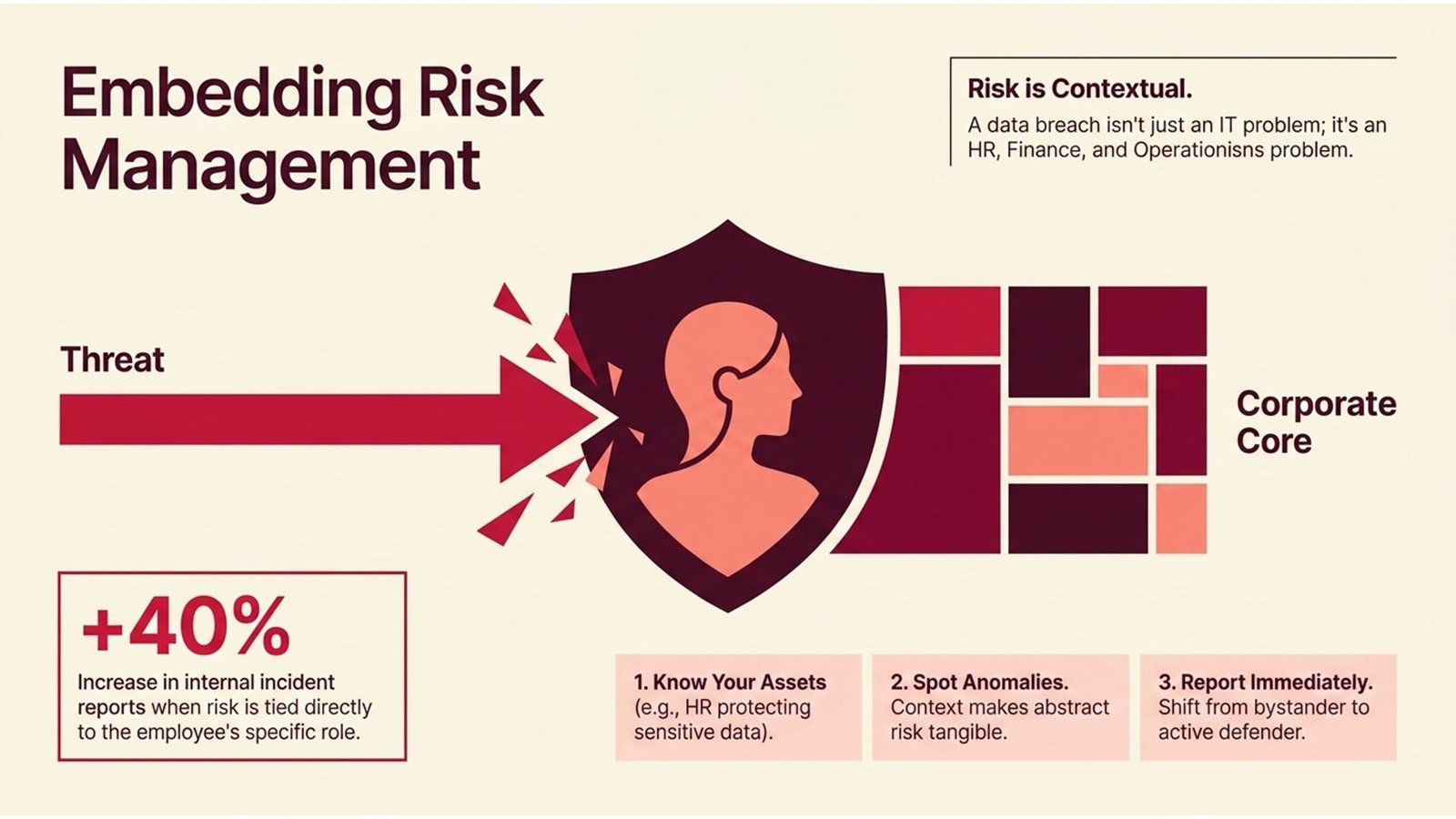
The aspect of cybersecurity cannot be isolated into a separate training session. To ensure that employees really internalize its significance, risk management training has to be integrated into the larger context of the way the organization functions. Employees gain a deeper, authentic interest in protection practices when they come to realize that a data breach will not only be a nuisance to IT, it can also lead to regulatory fines, loss of customers, and damage to reputation.
The first step in effective risk management training is to make the employees know what assets they have a responsibility to protect. An example of a human resources professional will deal with sensitive personal information on a daily basis. A specifically designed data classification, data access controls and safe data disposal training, with a framing of such training within the HR context, is exponentially more effective than a generic data protection training lecture. It is this contextual anchoring that brings the abstract concept of risk to reality.
Better incident reporting cultures are also enjoyed by organizations that incorporate the principles of risk management in their e-learning programs. By making employees aware of risk in terms they can relate to in their respective roles, employees will do a better job of raising red flags when unusual activity is detected sooner than otherwise. In Germany, a logistics company incorporated risk management training into its onboarding program for warehouse workers, teaching them how to identify abnormalities in patterns of system access by warehouse workers. The company has registered a 40 percent growth in the number of internal incident reports within six months, which allowed the security team to work on the potential vulnerabilities before they rose to high levels.
Table 2: Employee Risk Levels and Recommended Training Intensity
| Employee Role | Risk Level | Training Frequency | Key Topics |
| General Staff | Medium | Quarterly | Phishing, password hygiene, and device security |
| Finance & Accounting | High | Monthly | Invoice fraud, data handling, and access controls |
| IT & Developers | Very High | Monthly + Ongoing | Insecure code, insecure code management. |
| Executives & Management | High | Quarterly + Simulations | Social engineering under attack on decision-making. |
| HR & Payroll | High | Monthly | Privacy of the data, insider threats, and identity authentication. |
Five Key Steps to Launching a Successful Cybersecurity E-Learning Program
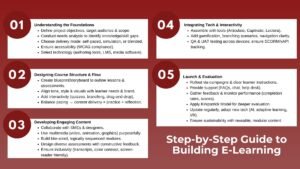
To develop a cybersecurity e-learning program that is effective and can be used to alter behaviors, it takes more than just buying an off-the-shelf platform. The five steps that follow are a systematic approach to getting a junior or mid-level professional to embark on the process of launching or enhancing the e-learning training efforts within its cybersecurity program by its junior or mid-level professionals.
Step 1: Conduct a Training Needs Assessment. Prior to creating any content, map the particular threat landscape that is pertinent to your organization and pinpoint knowledge gaps by role. Quality inputs include surveys, interviews with team leads, and a review of past security incidents. This evaluation will ensure that the program will be responding to actual vulnerabilities and not general issues.
Step 2: Define Clear Learning Objectives. A measurable outcome should be in each module. A clear objective is that employees will properly identify and report a simulated phishing email within 24 hours of receiving the email. Specific goals facilitate easy measurement of the effectiveness of the program.
Step 3: Develop Role-Based Learning Paths. Divide employees into the functional divisions and develop interactive e-learning material in each department to fit their unique human resource requirements. The paths based on roles decrease cognitive overload and enhance relevance, which enhances knowledge retention.
Step 4: Integrate Risk Management Training Throughout. Risk education should not be considered an independent course. Integrate risk management training with each topic – such as password management, email security, and mobile device usage – so that the employees will always relate what they are doing to organizational risk.
Step 5: Measure, Iterate, and Communicate Results. Continuously improve the program using platform analytics, phishing simulation data, incident trends, and more. Publicly distribute share results with the leadership and employees. Once individuals perceive that their training activities are lessening the actual risk, the level of engagement increases.
Process Flow 1: Cybersecurity E-Learning Implementation Lifecycle
| Phase | Activities | Key Output | Timeline |
| 1. Discovery | Needs analysis, threat analysis, and interviewing stakeholders. | Gap Analysis Report | Weeks 1–2 |
| 2. Design | Formulate the learning goals, draw up the role-based tracks, module storyboard, and module script. | Learning Design Blueprint | Weeks 3–5 |
| 3. Development | Construct interactive modules, phishing simulations, and tests. | Completed Course Library | Weeks 6–10 |
| 4. Deployment | LMS configuration, registration of users, communications strategy, and pilot test. | Live Training Program | Weeks 11–12 |
| 5. Evaluation | Tracking of completion, results of simulation, knowledge test, and iteration. | Performance Dashboard | Ongoing |
Process Flow 2: Incident Response Learning Pathway for Employees
| Stage | Employee Action | Supporting Training Module | Escalation Point |
| Detection | Identifies suspicious email, link or behavior. | Phishing Awareness & Social Engineering | Flag to the line manager |
| Containment | None of the above will work, and will switch off the network when asked to. | Safe Browsing and device Security. | Reporting through the incident portal. |
| Reporting | Reports an incident with details. | Incident Reporting Procedures | IT Security Team |
| Review | Attends debrief/ refresher module. | Post-Incident Learning Module | HR / L&D Team |
| Reinforcement | Attends further specific training. | Training: Role-Specific Risk Management Training | Training Completion Logged |
Challenges, Lessons Learned, and Sustaining a Security-Aware Culture
Regardless of how well-designed cybersecurity e-learning training programs are, they are not without usual challenges. Low completion rates, fatigue by the learner, lack of leadership support, and difficulty in demonstrating ROI are issues that learning and development professionals often have to deal with. It is the proactive approach to these issues instead of a reactive one that makes the difference between programs that have a long-lasting impact and those that become mere background music.
Among the greatest lessons organisations learn is that compulsory training in the absence of internal champions hardly ever achieves success. After the department head is actively involved in the modules, speaks about security practices in the team, shares his/her own results of phishing simulations, and takes an active part in the module, the completion rates and the sincere engagement will follow. A United Kingdom retail group had a 91% program completion rate in the first quarter of launch, which it attributes to much of its success being due to store managers framing the training as a team challenge, rather than a corporate requirement.
To ensure that engagement is maintained in the long-term, one should have a content refresh strategy. Cyber threats change every day, and the training modules that were developed 2 years ago may not be relevant to the current threat landscape. To create a program that integrates the review of the content monthly or quarterly, organizations should build a quarterly content review within their program calendar and update scenarios to reflect recent incidents – either global events, such as ransomware attacks on healthcare organizations, or industry-specific patterns of fraud. This makes interactive e-learning materials up to date and it helps to drive the point that cybersecurity is a dynamic discipline, and not a fixed list. By combining new material and risk management training refreshers ensures employees remain calibrated to the organization’s evolving risk posture.
Conclusion and Actionable Insights
The ultimate cybersecurity is a people problem, and the best solution that can be scaled to the maximum to help organizations achieve a resilient, security-conscious workforce is a cybersecurity e-learning training. The data speaks it all: programs that present interactive e-learning content, provide risk management training content in the appropriate context, and measure the results in a rigorous manner yield measurable results in terms of threat detection, incident reporting, and overall organizational security posture.
To the practitioners operating in this space, whether you are designing the very first program in your organization or you are making improvements to an existing one that has been in place for years, the following actionable insights can help provide a practical foundation to help you move forward:
- Begin with what is most important. Carry out an extensive needs evaluation prior to committing investments in either content development or platform licenses. The best initial step that you can take is knowing your unique risk landscape.
- Personalize as well as make training personal and relevant. Learning paths that are role-based and the modules based on scenarios significantly outperform generic content. Workers react when they are able to identify with the training content.
- Construct repetitions and reinforcements. One yearly training is not enough. Micro-learning modules, periodic phishing exercises, and periodic refresher courses are key elements of a long-lasting program.
- Prove the worth with statistics. Monitor the completion rates of the track, outcomes of the simulation, scores of the knowledge assessment, and trends of incidences. With this information, you can fine-tune your program and report the effect of the program to leadership.
- Cultivate security champions. Recruit and empower motivated employees in various departments to be excellent role models in promoting security practices and inspiring others. Culture change occurs within teams and not necessarily at the top.
The cost of the investment in well-designed continuous improvement of cybersecurity e-learning training pays off not only in risk reduction, but also in the creation of an organizational culture in which all employees know their part in ensuring that the business is not in danger. That culture can be your most valuable security asset in a threat environment that has not yet shown any signs of abating.